The PrintNightmare exploit is so scary, even Windows 7 got an emergency fix (but it’s imperfect) - mcdonaldgrot1995

Microsoft typically releases updates for Windows as part of its unit of time "Patch Tuesday" safety blitz, but the company took the unusual stride of cathartic an emergency out-of-band security update late Monday night to fix the critical "PrintNightmare" exposure published (and deleted) by researchers last week—even for Windows 7. Bottom line? Update your Windows Microcomputer pronto… simply the spell not fix all PCs if you'atomic number 75 connected to a local network.
PrintNightmare attacks the Windows Print Spooler service, which runs past default. "A unlikely codification execution vulnerability exists when the Windows Print Spooler service improperly performs privileged file operations," Microsoft's enforcement summary states. "An attacker who successfully used this exposure could run arbitrary code with SYSTEM privileges. An attacker could and so install programs; look at, change, or delete data; or create new accounts with full user rights."
In other words, PrintNightmare lets attackers into your system over the internet, then they essentially have free rein over your computer. "Every suspended editions of Windows are affected," Microsoft warns.
Microsoft released emergency protection patches for most versions of Windows 10, Windows 8.1, Windows RT 8.1, and various Windows Waiter installations. "Supported versions of Windows that do not have security updates available on July 6 will constitute updated shortly after July 6," Microsoft says. Driving home how severe this exposure is, the company even released a PrintNightmare security fix for Windows 7, an OS that was forced into retirement last year.
 Brad Chacos/IDG
Brad Chacos/IDG The company lists these patches as a temporary fix, and security measur researcher Matthew Love bite says that the patch only nullifies the danger of removed execution. That means that if an attacker manages to physically get ahold of your PC, they could still leveraging PrintNightmare to take control of information technology. (Update: After the patch was released, security researchers discovered that fully patched systems could still be attacked remotely if your administrator enables careful settings to enable a web printer feature called Full stop and Print, Ars Technica reports.) But for the vast absolute majority of people, simply victimization personal computers in their national, shutting down the ability for this exposure to act upon over the internet should effectively render it obsolete.
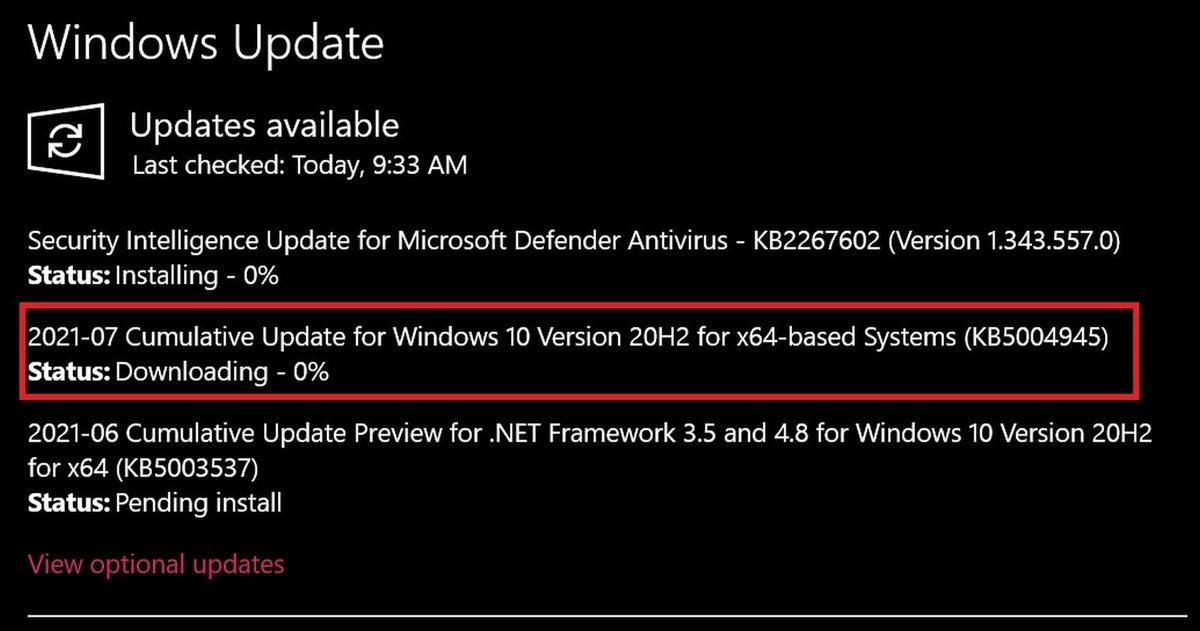
Thus get to downloading, folks. Checking Windows Update on my PC showed the PrintNightmare patch (KB5004945 for my version of Windows 10) already available. Piece you'Re organism safety-apt, make a point to instal an antivirus and perform the five easy tasks that supercharge your security if you haven't already.
Editor's mark: This article originally published on July 7, but was updated July 8 to mention that Point and Print could still leave fully patched PCs vulnerable to remote executing.
Note: When you purchase something after clicking golf links in our articles, we whitethorn earn a smaller commission. Read our affiliate link insurance for much details.
Brad Chacos spends his years digging through screen background PCs and tweeting as well much.
Source: https://www.pcworld.com/article/394840/the-printnightmare-exploit-is-so-scary-even-windows-7-got-an-emergency-fix-but-its-incomplete.html
Posted by: mcdonaldgrot1995.blogspot.com


0 Response to "The PrintNightmare exploit is so scary, even Windows 7 got an emergency fix (but it’s imperfect) - mcdonaldgrot1995"
Post a Comment